We Get You—and We Got You—in 2021
As we exit 2020, destined to be remembered as one of the most challenging years in our history, and enter 2021, we want to remind you that we are here for you. We get you, we got you, and we know what you’re going through—and you’re not alone. When our clients got focused on safety and security last year, they called us—maybe about the same things you’re struggling with:
- Got overwhelmed: Some clients have plans with no one to implement them, and others know they need to improve safety and security at their organization but don’t know what to do first, next, or at all. Serving as a Security Advisor, we help define what you have and what you need. From an assessment to an emergency management plan to training for your entire workforce or specialized sessions for your leaders, we can help you get your plan in place.
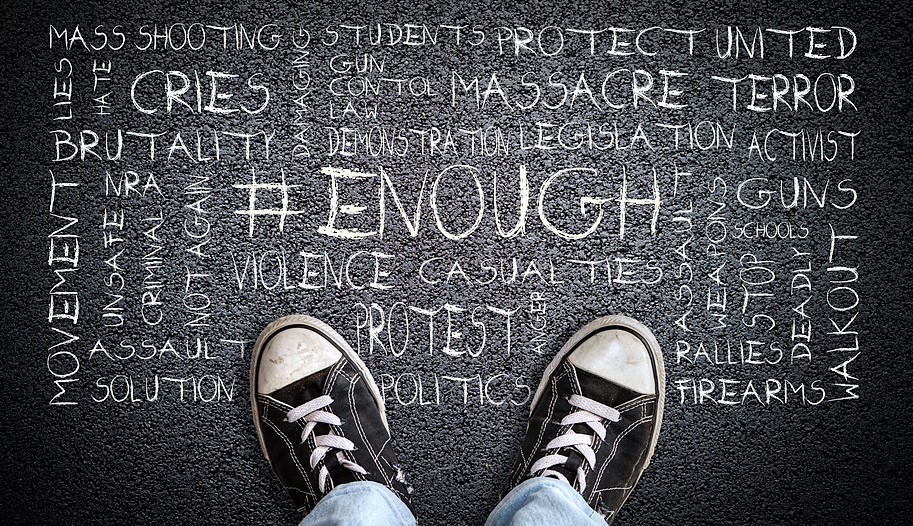
- Got ready: Workplace violence can affect every organization in every industry. And that makes a Workplace Violence Program, policy, and training even more critical to the safety of your employees. The program establishes your commitment to a safe and secure workplace, the policy strengthens your pledge to promoting employee well-being, and the training invites your employees to participate in and foster their own safety. Our client came with a vision of employee wellness that went beyond exercise or work life balance, and we helped them build a workplace violence program with safety and security at its foundation.
- Got together and got involved: Many of our clients do not have a Chief Security Officer or a security department at all, forcing security concerns to Human Resources, Legal, or Facilities. Our client wanted to move away from the siloed approach to security where different aspects were housed in different departments and focus their approach on a centralized system of threat identification, assessment, and management with Customized Training to ensure optimum risk management. While an informed and participative workforce makes every workplace safer, training with internal and external collaboration adds another layer of security that protects your employees.
- Got ahead and got protected: Not only does an Independent Security Study (ISS) of executive protection programs for high net worth people comply with applicable IRS deductible expenses—and save the executive thousands of dollars—it also protects the entire organization by looking at its overall security program. Our client understood the need to evaluate the specialized security requirements of the CEO and combine it with an assessment of the vulnerabilities impacting the entire organization. With a review of the security measures at the corporate offices, during transportation, and at private residences, you will understand where you are exposing employees to unnecessary risk.
- Got caught unprepared: Safeguarding employees was our client’s focus, and as you share that priority, especially in an emergency, a holistic Emergency Management Plan (EMP) ensures they will know how to hide, evacuate, communicate before, during, and after an incident, and resume normal business activities as you recover. An EMP that covers all hazards including natural (weather), accidental (fire), and intentional (criminal) incidents prepares your organization for the unexpected—even a pandemic.
We’re Here to Help
Have you got stuck, got caught off guard, got no one to turn to, or got lost? And would you like to get help, get support, and get going? Because in past years, when the going got tough, the tough got the LFG.
So let’s get excited about the “what ifs” of 2021. What if your employees felt safe and secure? What if you focused on your employees’ well-being? What if you found a trusted advisor who gets you—and takes your security to the next level? You’ve got that all in The Lake Forest Group. And we’re just a call or click away. Let’s get started.
Contact Mike at [email protected] or 312.515.8747 to discuss whatever is on your mind in a free 30-minute consultation and together we can create a strategy that supports and prioritizes your employees.