Conscientious and well-informed university personnel know that adequate staffing, multi-disciplinary involvement, sufficient resources, appropriate policies, and external support make these incidents less likely to occur—and make leaders more prepared if they do. Safe University (Safe U) partners with you to supplement and enhance your existing security programs by tailoring best practices to your unique situation and campus culture
Welcome To Safe University (SAFE U)!
YOUR PARTNER IN CAMPUS SECURITY
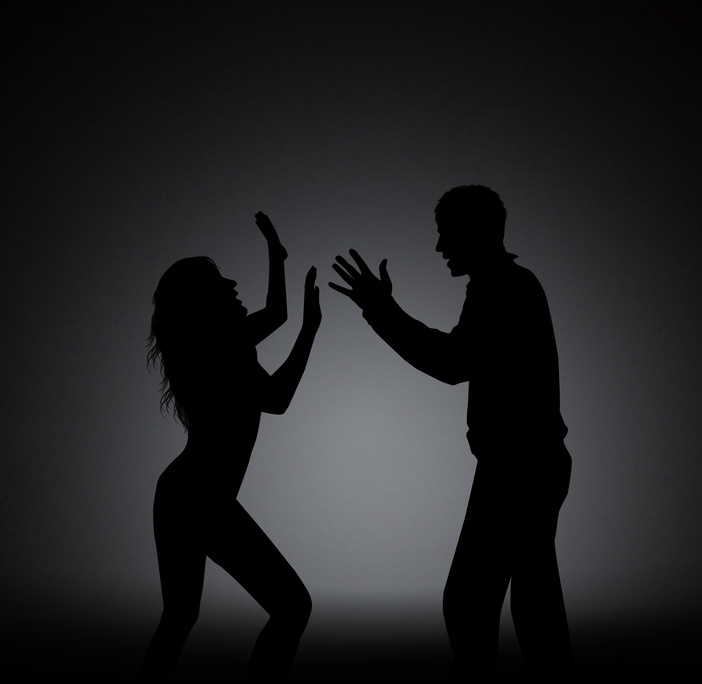
 When the safety of your people is one of your top priorities and your college’s reputation is one of your most valuable assets, you’ll do whatever it takes to provide a safe environment for your students, staff, and visitors. High profile incidents such as mass shootings and sexual attacks at several universities have put the topic of campus crime in the public eye today more than ever before.
When the safety of your people is one of your top priorities and your college’s reputation is one of your most valuable assets, you’ll do whatever it takes to provide a safe environment for your students, staff, and visitors. High profile incidents such as mass shootings and sexual attacks at several universities have put the topic of campus crime in the public eye today more than ever before.
HOW SAFE U BENEFITS YOUR SCHOOL AND YOUR PEOPLE
Our Safe U program specifically tailors best practices in these areas to your unique environment:
• Processes: policies, procedures, plans, and programs
• Personnel: management, police, public safety, and security
• Technology: cameras, access control, alarms, notifications, and call/assistance station boxes
• Emergency preparedness: weather, fire, power, and intruder
• Education awareness and training: classes, exercises, and web-based
• Event planning and management: school-sponsored functions
• Background screening and drug testing: scope, pre- and post-employment
• Physical security: fences, gates, barriers, lighting, and locks
• Regulatory compliance: Title IX, Violence Against Women Act, and Clery Act
PROTECT YOUR PEOPLE, CAMPUS AND BRAND BY BENCHMARKING WITH THE BEST
Studies show that although 86% of higher educational schools have an emergency operations plan, more than 1 in 4 have not had a hazard and vulnerability assessment to develop appropriate all-hazard emergency planning. We’ll share with you knowledge gained from safeguarding global corporations, high profile individuals, major events, and campuses around the country to protect what’s most important.
ADD ANOTHER LAYER OF SAFETY THROUGH SAFE U’S OBJECTIVE REVIEW
By providing objectivity through an independent analysis of your current resources, Safe U ensures a holistic security strategy by sharing the extensive expertise of our team. G. Michael Verden, CEO and Owner of The Lake Forest Group, is a global security expert with a distinguished 21-year career with the United States Secret Service. As a Special Agent, he served on the Presidential Protective Division, Dignitary Protective Division, and Counter Assault Team and assisted in the security and protection of facilities and people for major events, including the Olympics, Super Bowl, Kentucky Derby, Indianapolis 500, and the Women’s Soccer World Cup, among others. As Director of Security for the NBA, he supervised security for the NBA All-Star Game, NBA Finals, and World Basketball Championships. Mike will personally guide the Safe U program to assess and evaluate your current security needs and provide options to optimize your strategic security plan and emergency management plan.